From day one, the philosophy behind Dokky has been crystal clear: to offer a self-hosted, decentralized, clean, and lightweight collaboration platform, free from burdensome external dependencies. Today, with the official release of v2.2.0, we’re taking a step toward complete resilience and independence in your Document Distribution.
Welcome to the era of Dokky P2P.
Why the BitTorrent protocol in Dokky?
Anyone who runs a Document Distribution Platform knows that traffic and bandwidth can become a significant bottleneck (and cost). Traditionally, if a Document goes viral, the server has to handle every single download request, with the risk of overloading or increasing infrastructure costs.
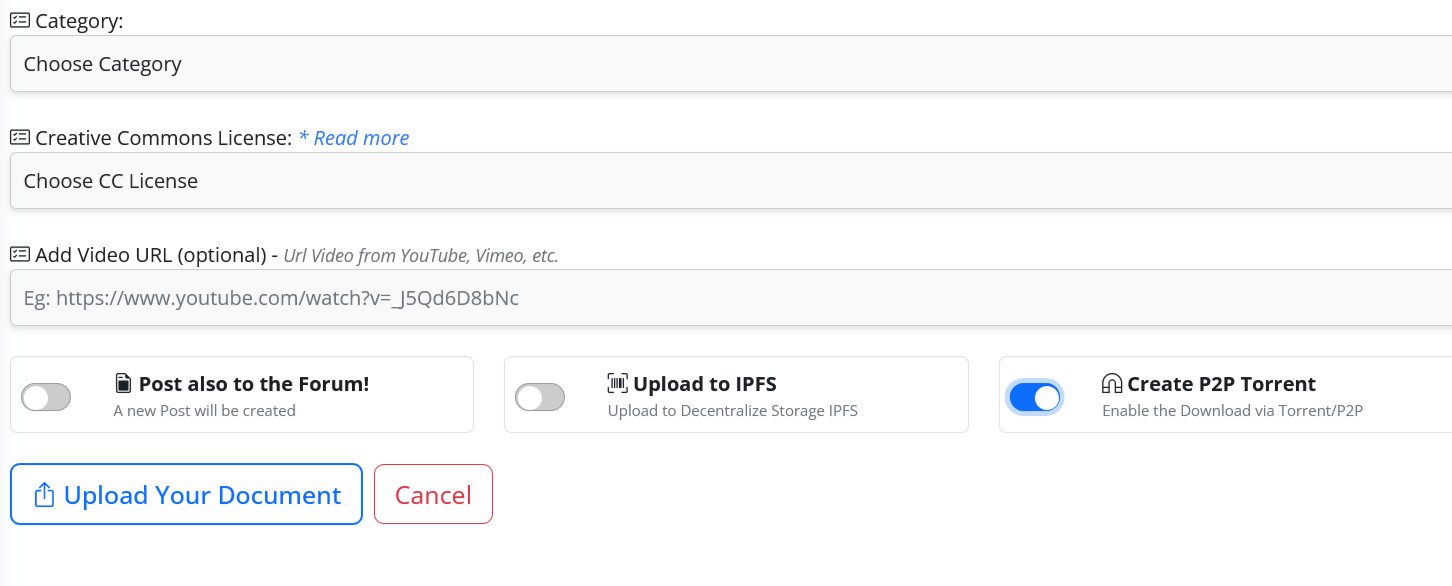
With the new native P2P module, Dokky embraces true philanthropic Decentralization and solves this problem at its root through three engineering pillars:
– Total Resilience: Documents no longer rely exclusively on the central server. Once they’re uploaded to the Torrent network, their availability becomes distributed.
– Native Web Seeding: By leveraging the HTTP-Source architecture, the Dokky instance itself acts as the initial source. This eliminates the classic “missing seed” problem in Torrent networks: users’ downloads will always start instantly, even if they’re the first to request the file.
– Integrated Tracker: Dokky doesn’t rely on external public trackers that could track data or go offline. It includes a well-coded native tracker written entirely in PHP that securely maps peers in real time, optimizing direct connections between platform users. Data retention is temporary, following GDPR guidelines.
If the administrator decides to activate the feature from the backend, the platform transforms into a highly efficient mass distribution ecosystem, perfect for businesses, independent publishers, or research communities.
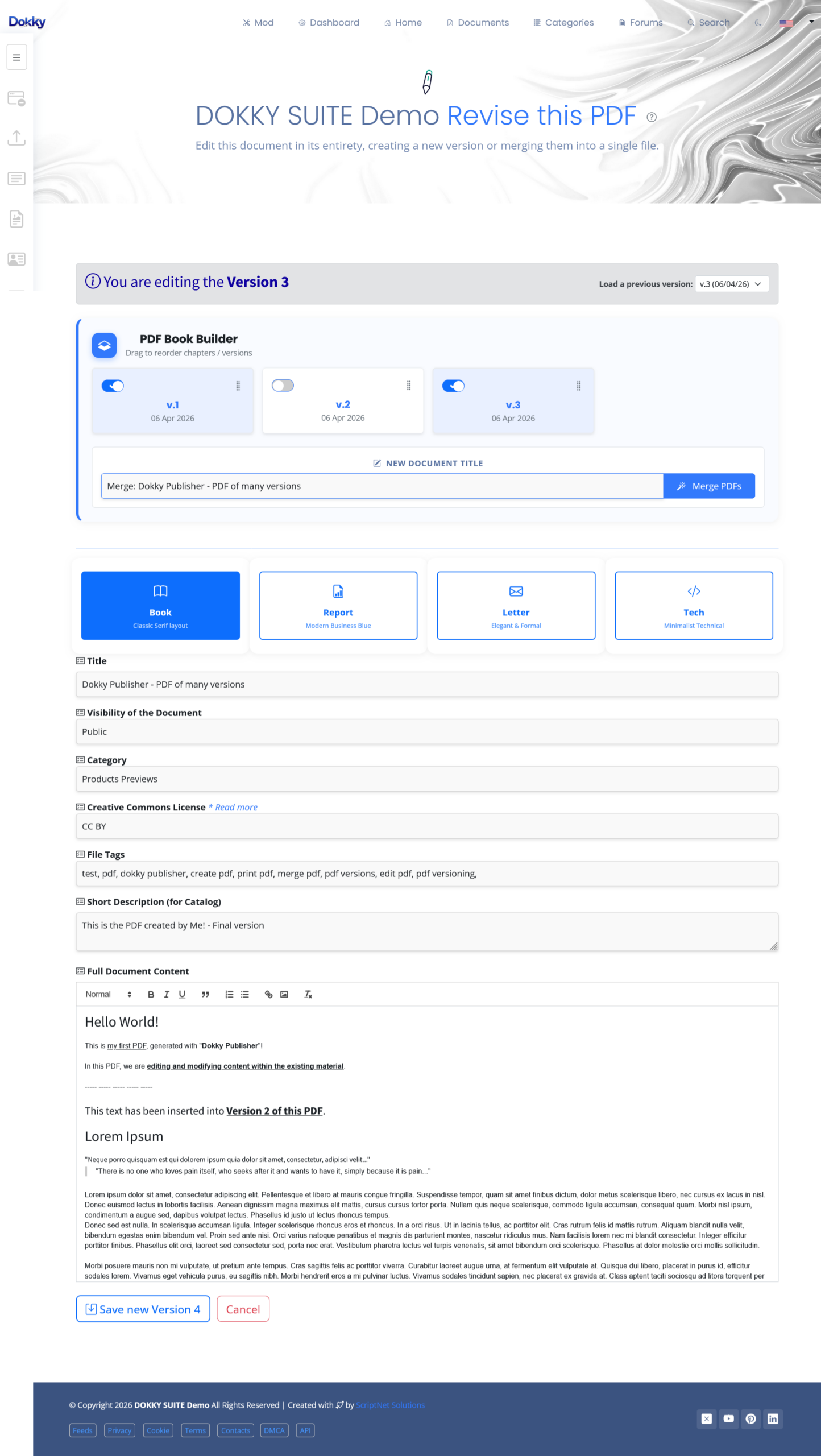
This release represents the latest in a highly intensive development journey that has radically transformed our suite over the past few months. The penultimate major step was taken with v2.1, a monumental release focused on core editing: we introduced Dokky Publisher, the native and fully self-hosted PDF creation engine (without any external API), complete with 4 professional layouts, lossless document lifecycle management, ISO 19005-3 (PDF-A3B) compliance, and the ability to merge multiple versions into a single, independent PDF eBook.
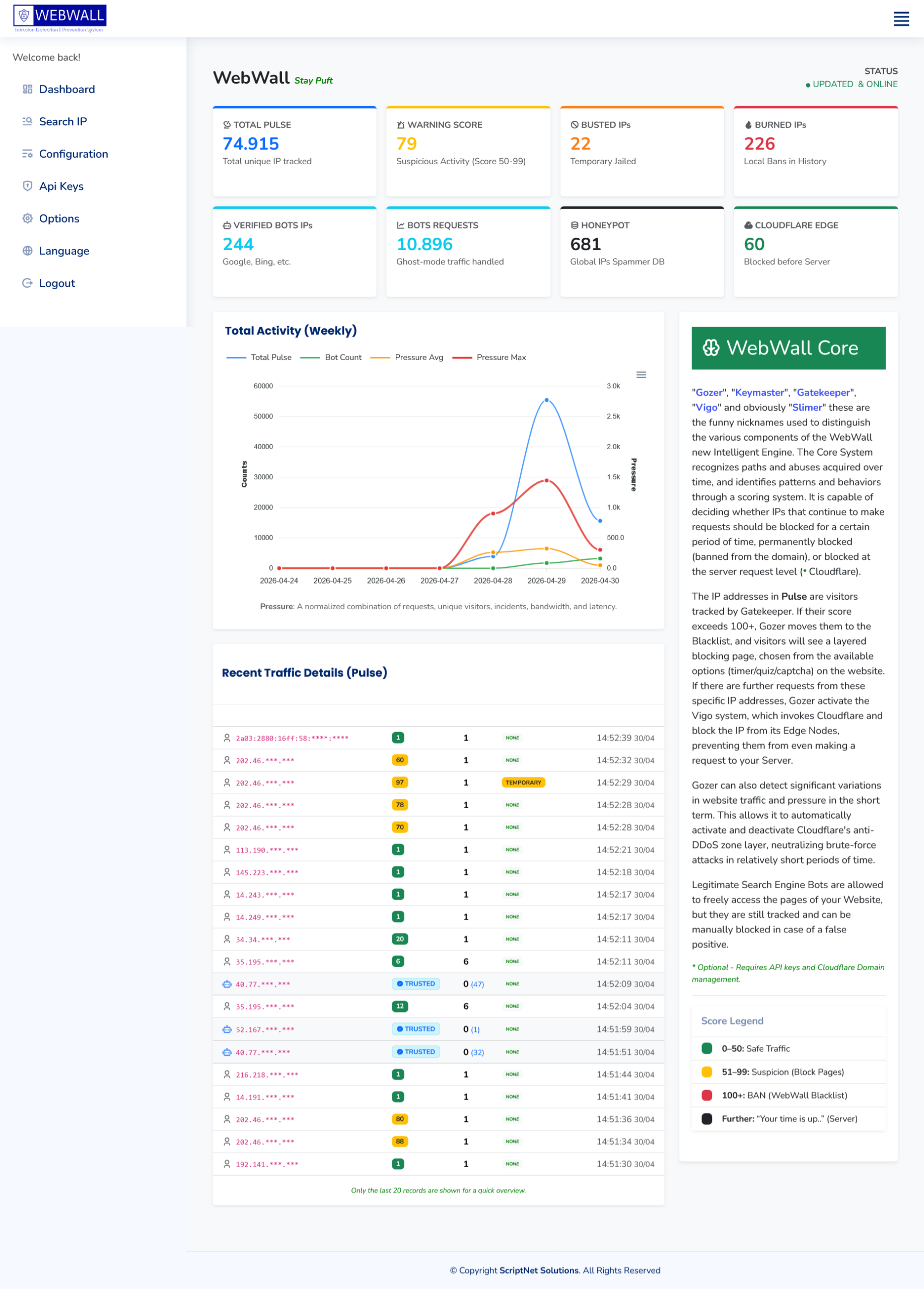
Today, with v2.2, we’re closing the loop by combining all this publishing power with the resilience of the P2P network, simultaneously updating the native WebWall module to v2.1 and revamping the administration interface.
A Powerful Technology That Requires Responsibility
The Decentralized nature of the BitTorrent protocol brings with it a fundamental dynamic that every user and administrator must fully understand. So, let’s conclude with an important note on privacy and data management: Once a document is shared via the P2P system, it is released into a network of independent nodes. Even if the original document is subsequently deleted from the Dokky platform (resulting in the automatic removal of the associated .torrent file on the server), it is not technically possible to delete or recall the peers and copies of the file already present within the network of users who downloaded it.
This feature represents an extraordinary weapon of freedom for the dissemination of knowledge, but it must be used absolutely responsibly, in full compliance with copyright laws and document ownership rights.
Clean, Lightweight, Independent
Every single line of the code written for this update faithfully upholds the promise of our architectural manifesto: Clean PHP, transparent code, and zero superfluous dependencies. Dokky requires no massive external libraries to handle bencode encoding or file tracking; everything runs natively on your server, guaranteeing you absolute control over your data, your privacy, and your operational costs.
Dokky v2.2.0 is ready. Update your instances, activate the P2P module, and unleash the full potential of your documents!

 .
.